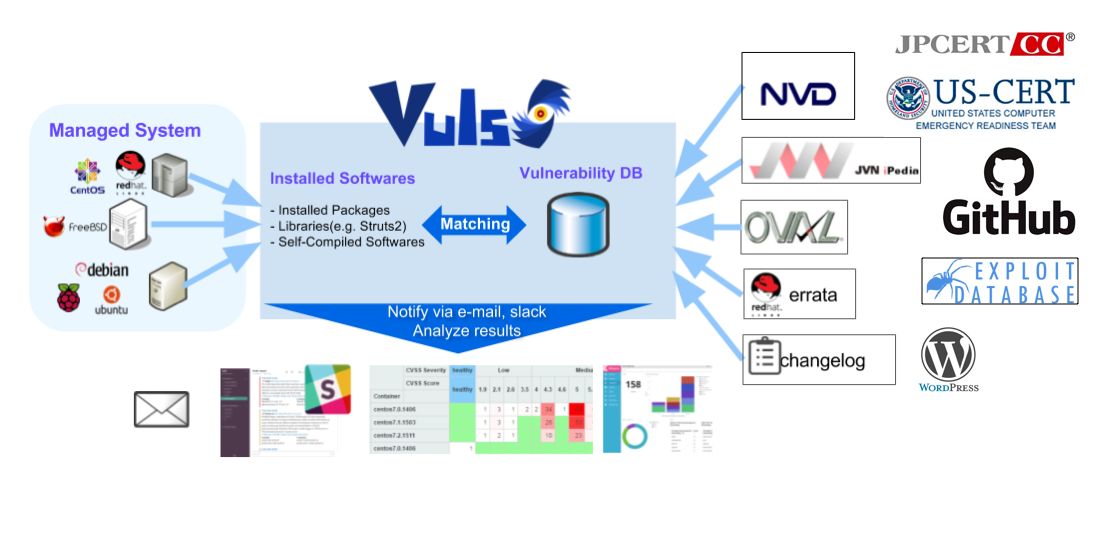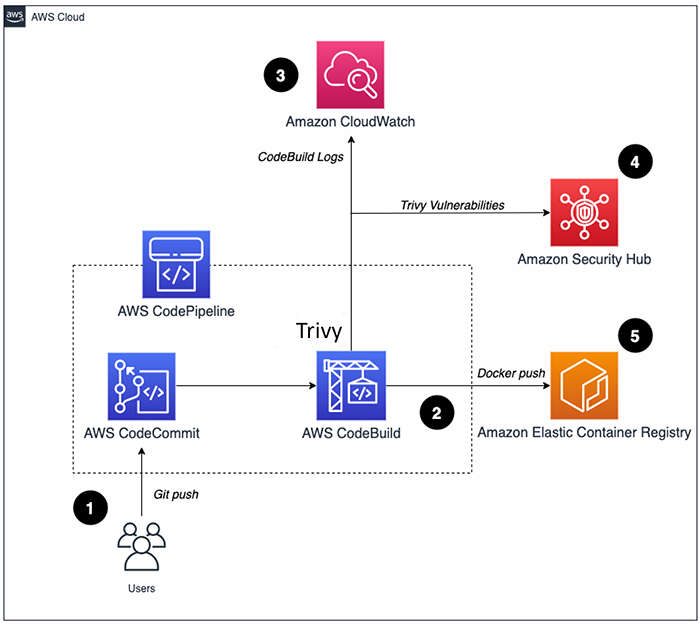
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog
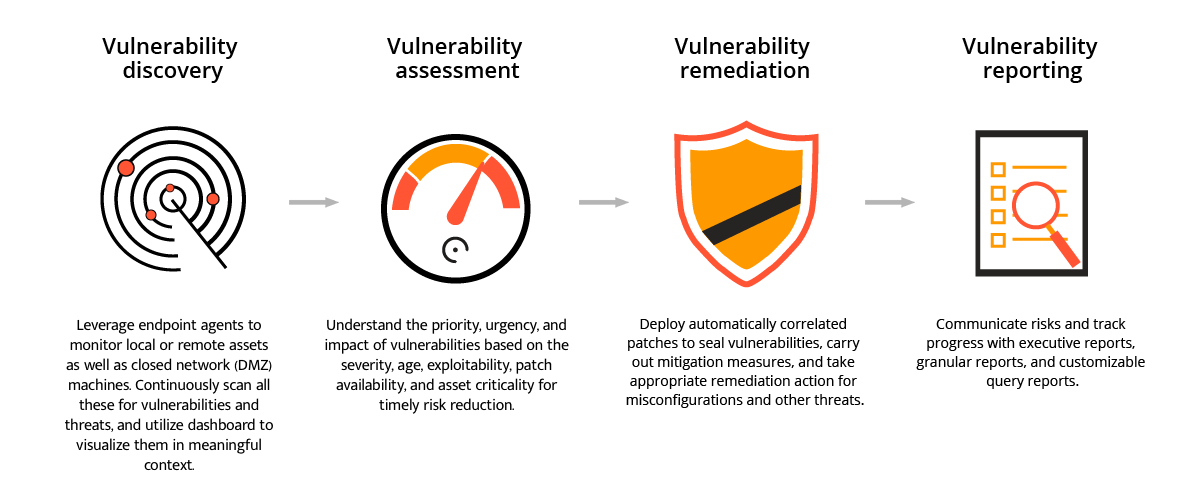
Introducing VMware Carbon Black Cloud Endpoint Vulnerability Management - VMware Security Blog - VMware

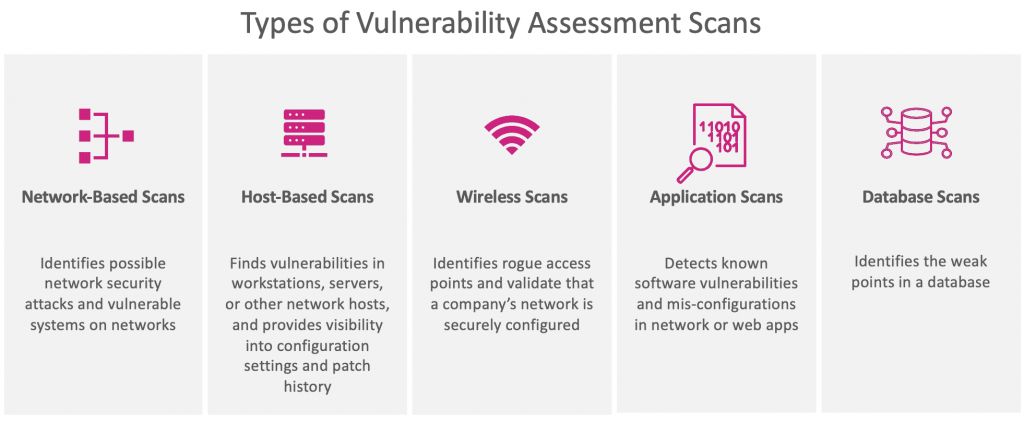
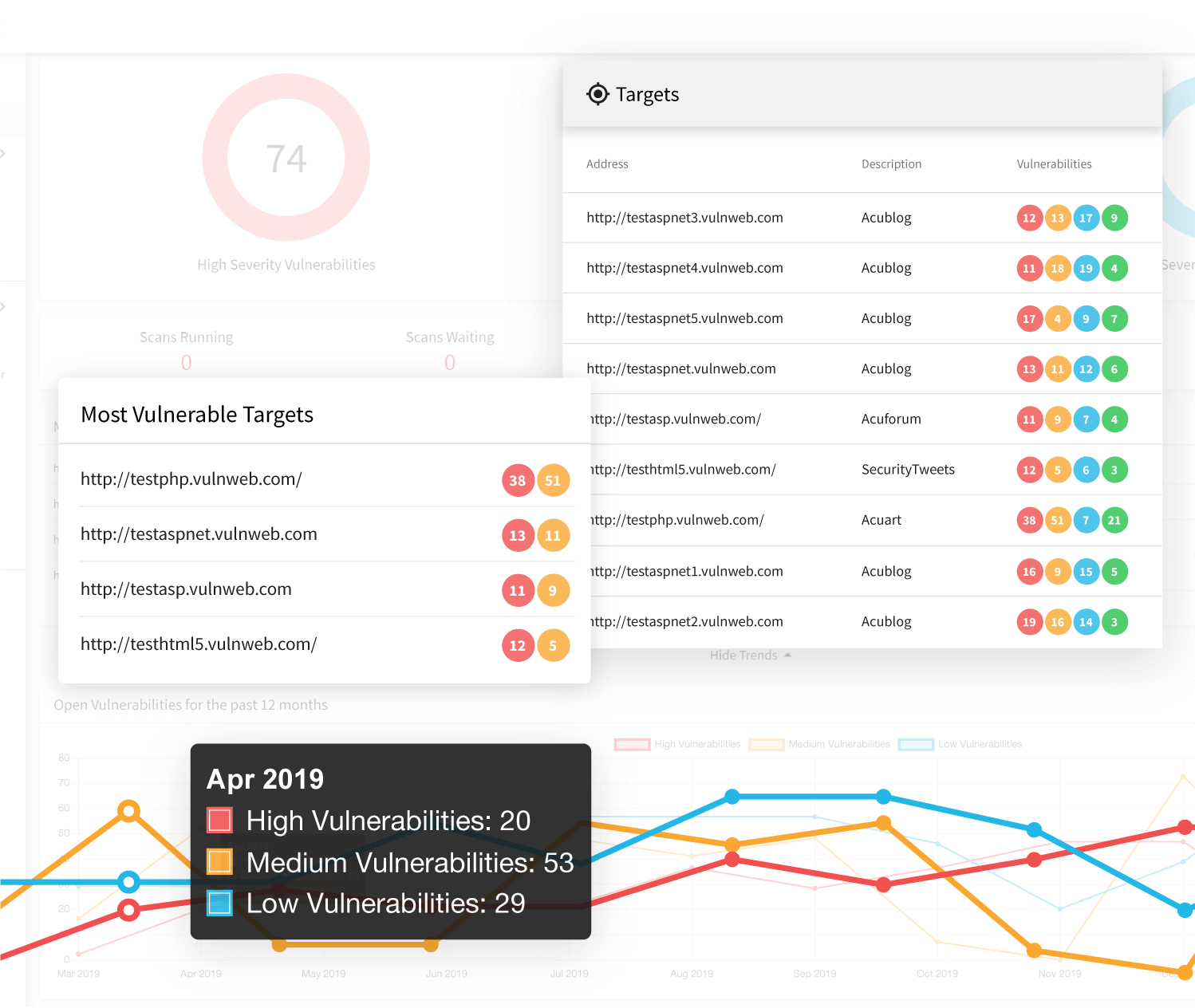
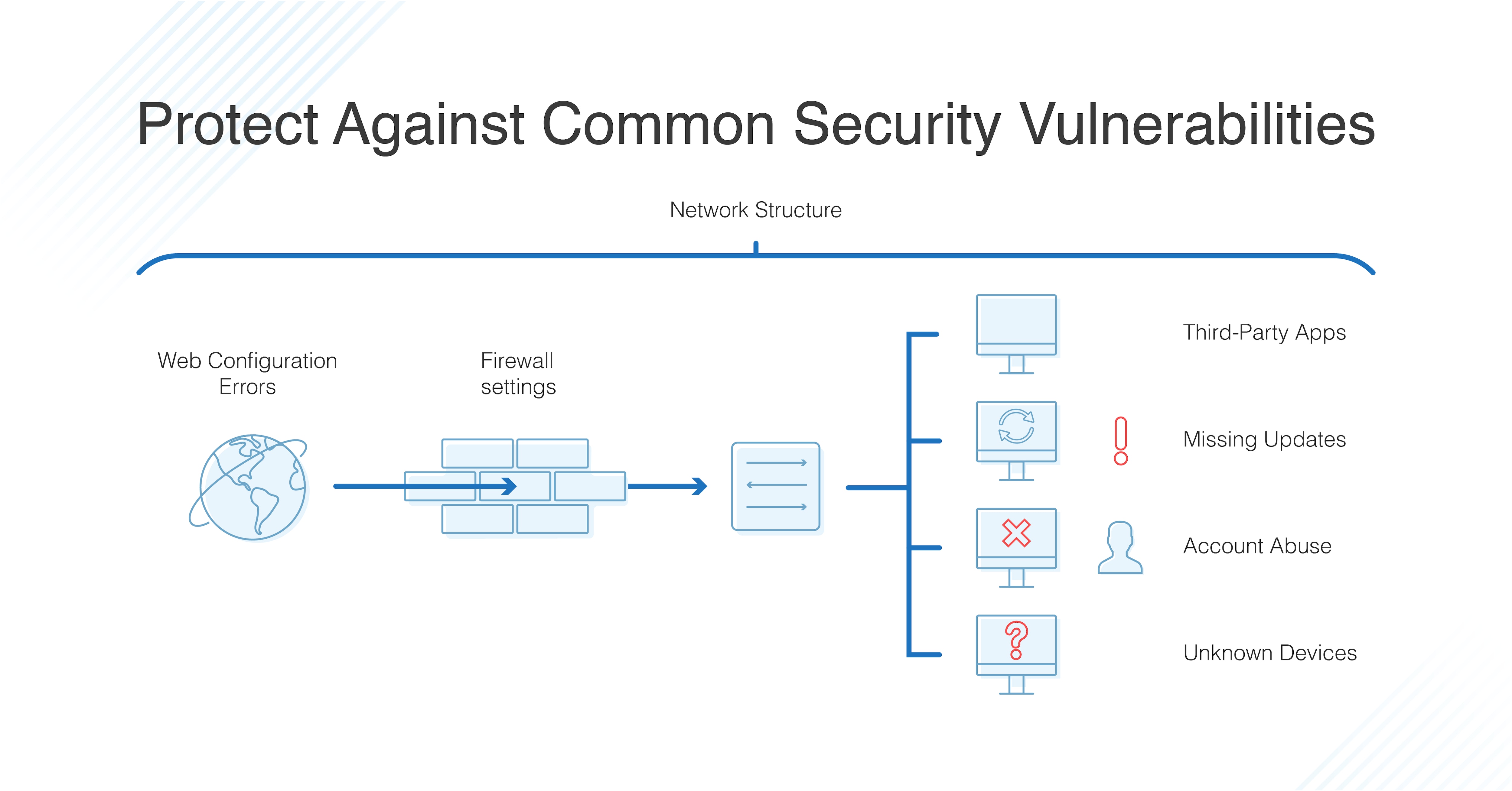
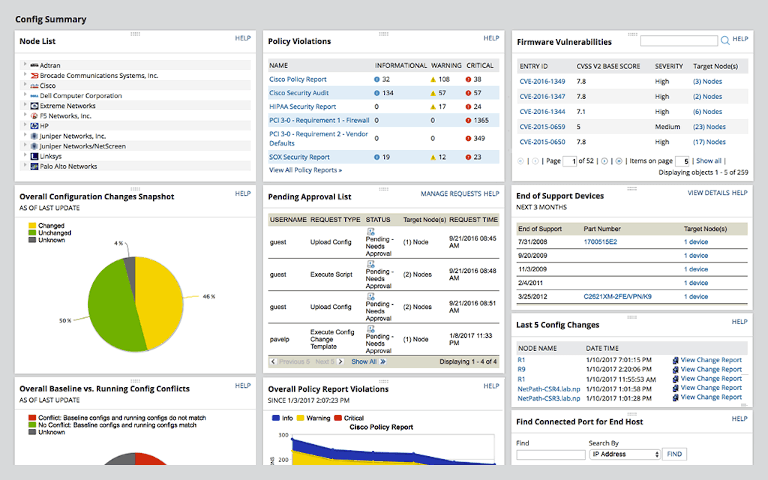
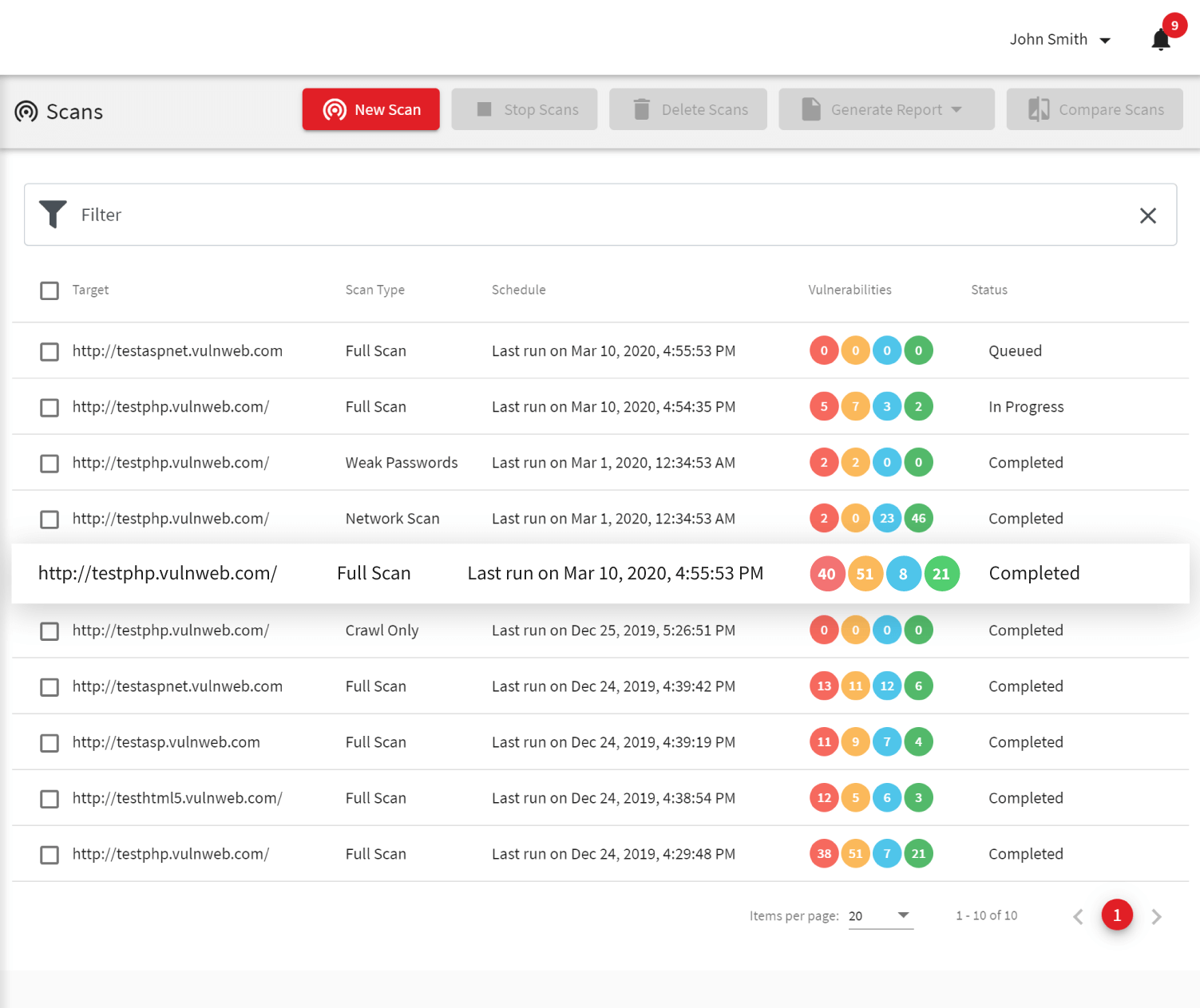
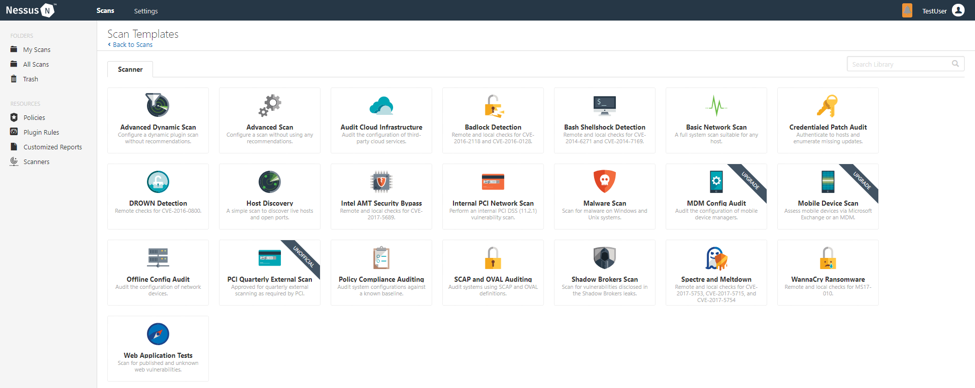
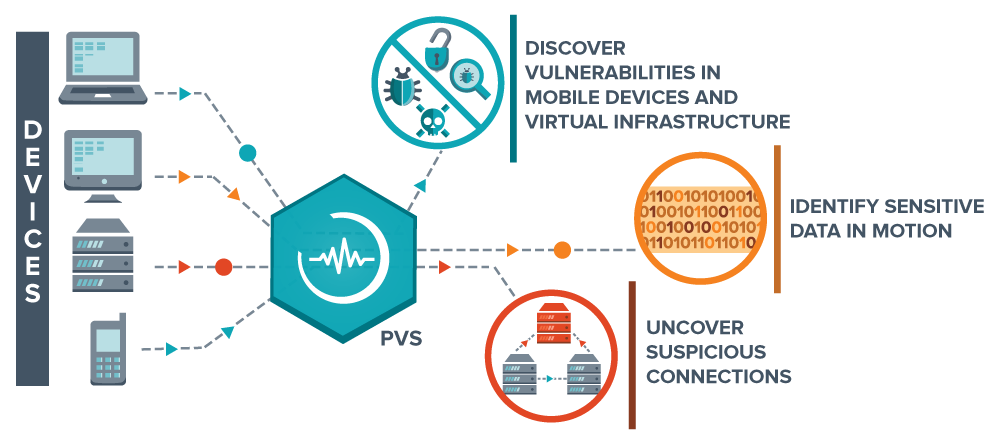
A survey on vulnerability assessment tools and databases for cloud-based web applications - ScienceDirect
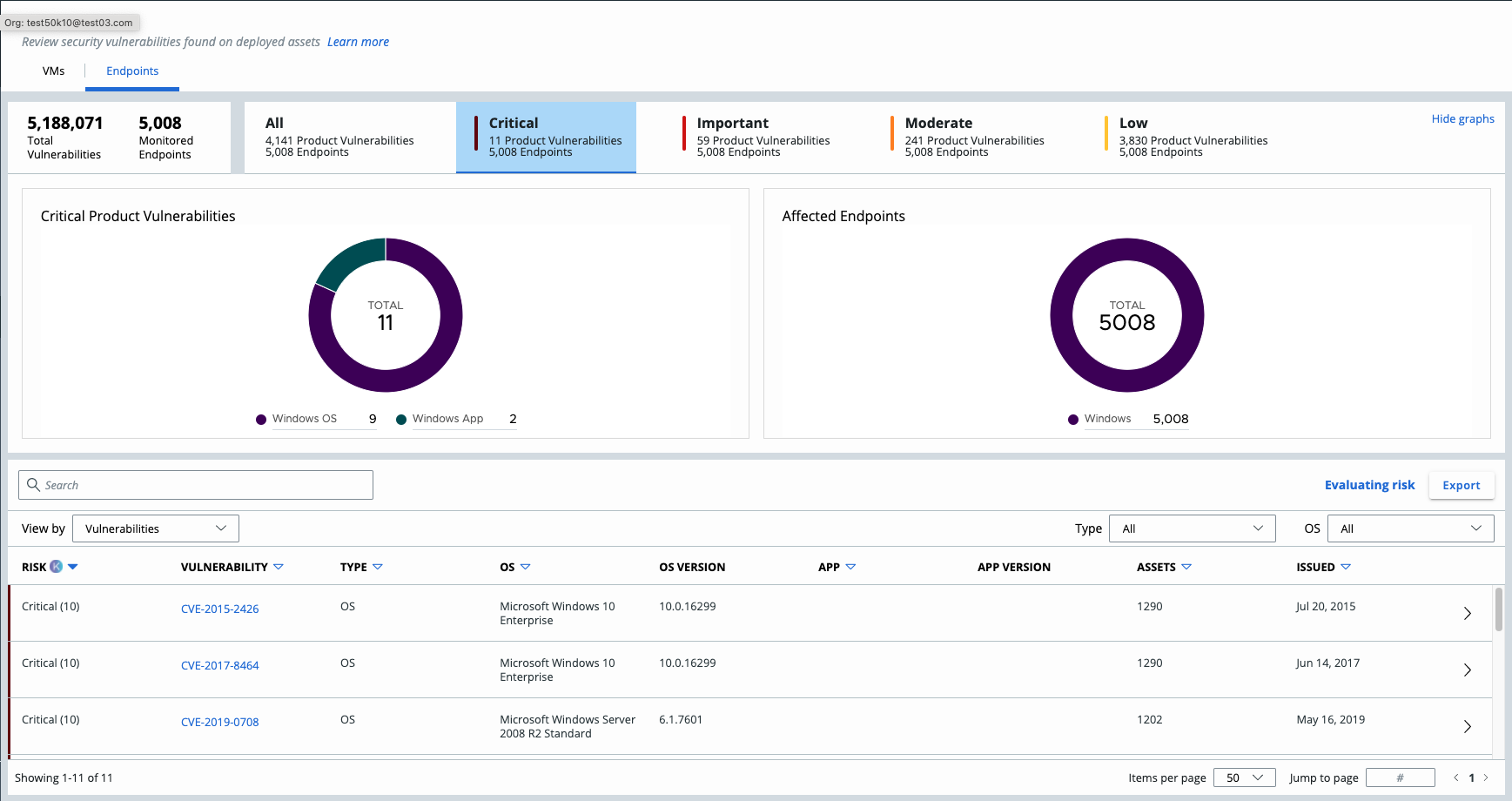
Vulnerability Scanner | Vulnerability Scanning Tools & Software - ManageEngine Vulnerability Manager Plus